Real Fake Tech Support - Beyond Pop-ups
Updated
Most of us are familiar with those annoying alarming pop ups that come up telling us something is wrong with our computer or that we have a virus and to call “this” number for help. Because we all know this old trick, cyber criminals have come up with even more ways to try and fool us.
The Real Fake Website
Have you ever accidentally mistyped the name of a website and ended up on a real website anyway? This is probably the easiest ones cyber criminals rely on since it is so easy for all of us to make this mistake. Here’s how it works:
You’re trying to contact the Geek Squad from Best Buy and visit their site by typing, "www.betsbuy.com."You see the Best Buy logo, find the support number, and call…and now they got you.
See, You went to betsbuy instead of bestbuy and landed on a site owned and made to look like the real site by cyber criminals. They have a support number for Geek Squad but it’s not really going to Geek Squad. It’s going to a cyber criminal ready to offer you fake support. All you need to do is give him access to your computer and a credit card!
The Real Fake Phone Number.
Search engines are our friends. Billions of us use them every day to quickly find just about everything. Criminals are relying on this too and they are waiting for us!
You search for tech support and a ton of options are at your fingertips. You don't have time to go through all of them so you click on the one of the first few you see. Cyber criminals know this and market these listings to show up first in search engines. Then, they just sit by the phone and wait for the call…..from you. All they need is remote access to your computer and your credit card information to fix it for a fee. Not only do they have access to your money, they have access to anything on your computer and free range to add whatever files they want as well….like viruses….or spyware. Scary stuff!
The Real Fake Business on Google Maps.
It is way too easy for scammers to add a legitimate looking business listing on Google maps. They’ll use the real location and website but will use a phone number that is fake. I’m pretty sure you know what happens after this!
Though Google typically verifies if a business is legitimate by mailing a postcard, calling, or emailing a numerical code to enter into a Google website, the system is easy enough for scammers to bypass with fake addresses and phone numbers.
Real Fake Emails & Text Messages.
Yes, the cyber criminals are here too. Why? Because that’s where WE are! Similar to spam texts and emails, they’ll send you a link or phone number to call to get tech support help.
Real Fake Phone Calls.
They call YOU! - Now that pretty much most of the population has cell phones vs. landlines, the criminals have begun targeting you via a phone call. Just because your number may not be published, doesn’t mean you won’t get a call. These criminals have auto dialers that dial numbers at random and people are on standby waiting for anyone to answer. When you do, they claim they are from “The Apple Care Team” and they received an alert that your cell phone or computer is infected. They offer to help and if you take them up on it, they got you.
Real Fake Browser Extensions.
Extensions are made to make our browsing easier. There’s some that track spending and offer discounts, grammar helpers, and now....real fake browser extensions. They can offer tech support at the click of a button or download malicious software when you install them. Either way, verify the publisher of any extensions you download and make sure they come from the Google Web Extension or Safari stores.
Oh, how the scammers love to scam, let us count the ways (and keep counting)...The important part is making sure you have the cyber security awareness necessary so that you can use your knowledge to your advantage to prevent these scams. (and save your hard earned cash)
Tips to Stay Safe
- We all get knocked in the arm by a kid or a cat while typing at some point but always check your spelling.
- Be mindful of the site(s) you are visiting and if something doesn’t look right, don’t click around. Verify its legitimacy first. Look for differences in the logo, grammatical or spelling errors, unbelievably free or very low priced items, phone numbers that don’t match the actual phone number to the company. If you still aren’t sure, contact the company.
- Always go directly to the official website to obtain the phone number. Don’t call a number you saw on an ad or got by email, etc.
- If something is wrong with your computer and you know a trusted friend or family member that knows how to fix them, it may be worthwhile to ask them for help.
- If you need to, call the store you purchased the computer from or call Microsoft or Apple for issues with their operating systems. Just make sure you are calling the correct numbers!
- Do your part for your fellow humans and report fraudulent activity. Let's team up and stamp these criminals out!
- Block the scam phone number that called you and report the number to the FTC.
- Do not install any apps if you are not sure who the publisher is.
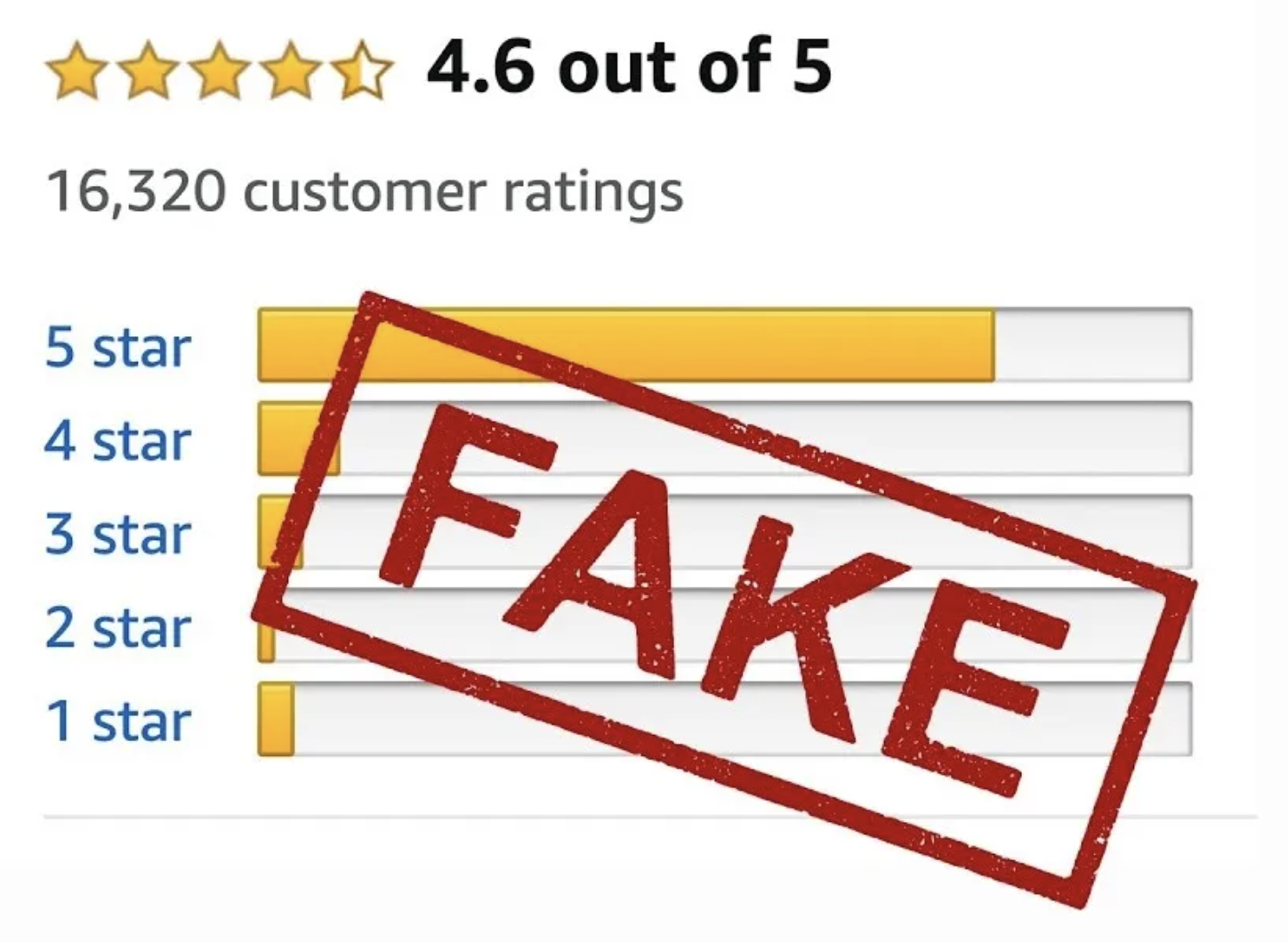
- Read a few reviews that have been verified from businesses when searching on social media sites or map services like Google Maps.
- Did you get a link sent to you for a support site? Instead of typing it into the address bar, type the link without the www into your browser's search field to see what comes up. You can even type the word "scam" after it to see if anyone else has complained about it!
- A legit help desk support team will not call you with an issue and they will not ask for your credit card information.