Wizer CTF: Secure Code Training for Developers
We're flipping the script on security awareness training for your dev team! How?
Boost your coding skills with our top-notch Secure Code Training for Developers. Immerse yourself in the art of breaking things, as we guide developers to better understand vulnerabilities and craft robust code. Our offerings include 15 new, in-depth video training sessions. Additionally, for coders seeking an extra challenge, explore our Wizer CTF Challenges. Elevate your coding abilities with our dynamic and engaging training methods for secure code development.
What is a Wizer CTF Challenge?
Engage in a digital treasure hunt with our Wizer CTF Challenges – an integral part of our comprehensive Secure Code Training. In these Capture the Flag (CTF) competitions, participants explore hidden text ("flags") by skillfully manipulating source code. Whether you're driven by friendly competition or a desire to enhance your coding skills, our Wizer CTFs offer both in a developer-friendly environment.
Designed to be both competitive and educational, our CTF challenges are tailored specifically for developers. The primary goal is to provide hands-on exploration, enabling development teams to learn and refine their coding practices for enhanced security. Picture reducing vulnerabilities and minimizing bugs before launching your code – an invaluable advantage for any developer. As our founder Gaby emphasizes, "Secure code is quality code." Join us in this dynamic quest for secure coding excellence.
How Does It Work?
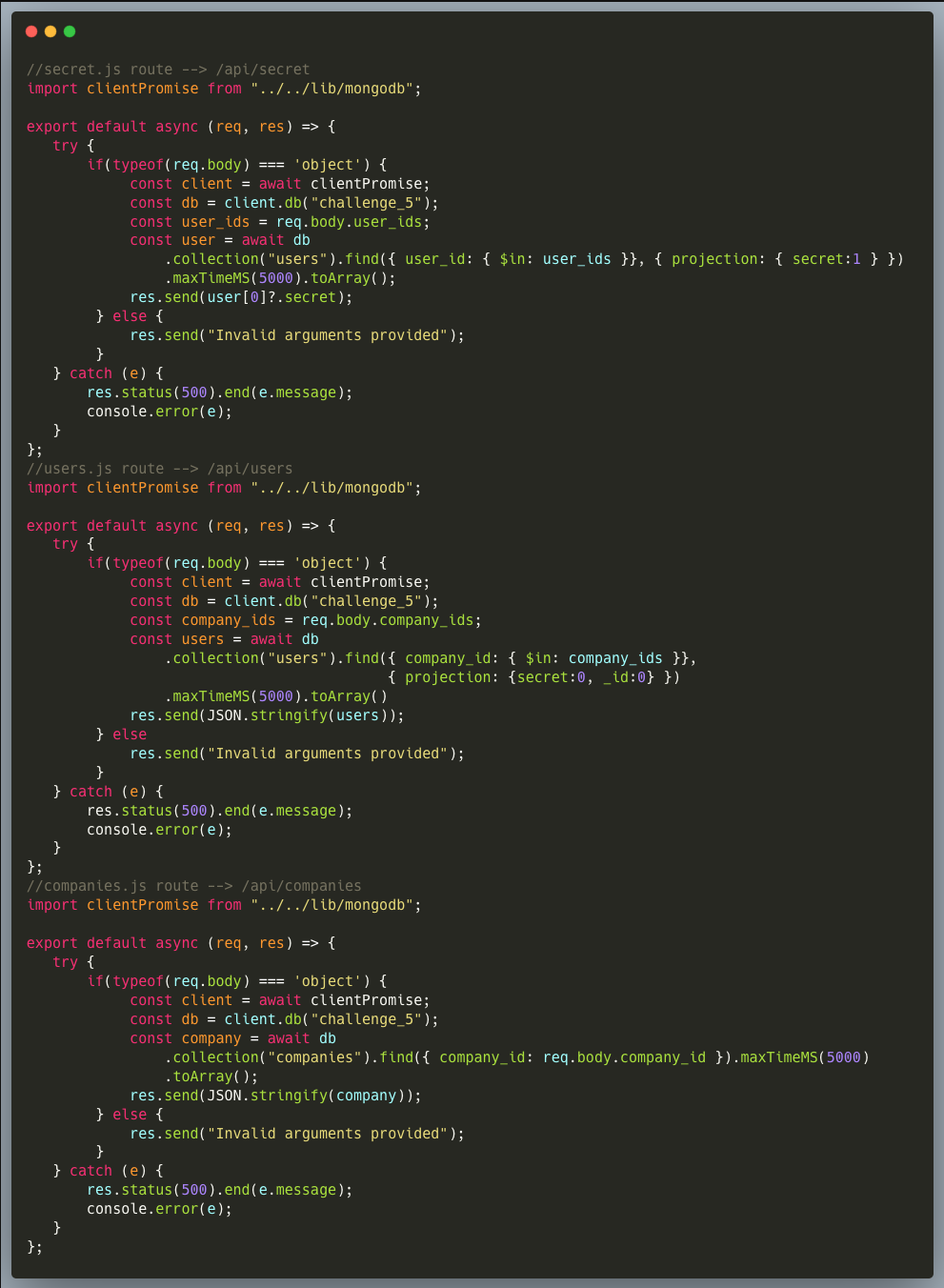
Discover the mechanics of our secure code training with Wizer CTF Challenges. Experience the excitement of six live challenges at any given time, refreshed bi-weekly for a continuous learning journey. Upon each new release, the oldest challenge gracefully retires, accompanied by insightful takeaways from Wizer's CTO, Itzik Spitzen.
Our CTFs blend education with enjoyment, ensuring broad relevance. Currently centered around JavaScript, each challenge presents a unique complexity, offering diverse learning opportunities with every release. Explore the dynamic world of secure code training with Wizer's engaging and evolving CTF Challenges.
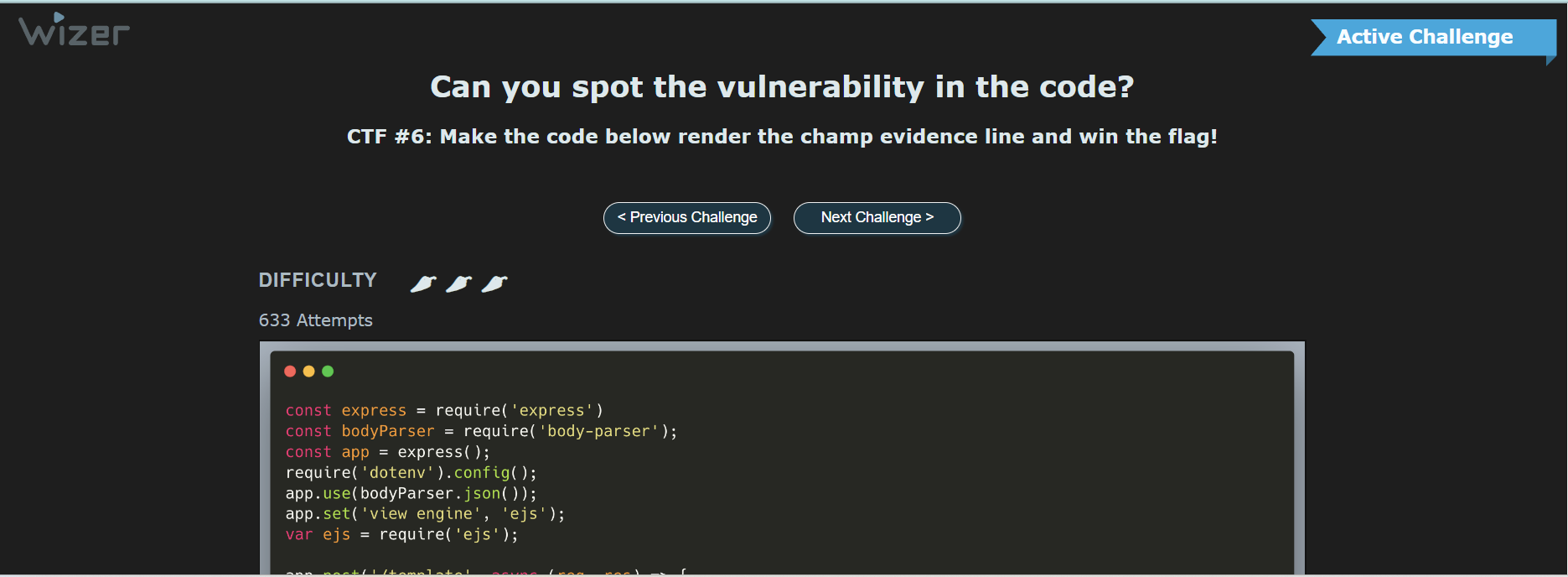
When you land on a new challenge, you'll see:
- How spicy the challenge is (aka difficulty level)
- How many attempts have been made to that point
- The coding challenge
- The area to drop the payload
- Public leaderboard
There's also an opportunity to share with your colleagues and an invite to join the community on our Discord server to hash out trouble issues and find support.
Unveiling the Secrets: Do Writeups Spill the Beans?
As clarified earlier, when a challenge takes its bow and is marked as 'retired,' the leaderboard may freeze, but the puzzle remains open for exploration. However, the retired challenge comes with a carefully crafted writeup – not a direct giveaway of the solution, though. Where's the thrill in that? We're committed to preserving the excitement for those who tackle it later.
Instead, the writeup serves as a valuable recap, reinforcing the key lessons the challenge endeavors to teach. Gaby and Itzik enhance this learning experience further with a live recap, adding a touch of interaction for those who prefer it. Dive into our first CTF writeup here or catch a glimpse of the recorded live session below. Join us as we unravel the world of secure code training with insightful recaps and engaging interactions.
Embark on the Secure Code Training Adventure: Who's Welcome?
Eager to test your skills? Our CTFs warmly welcome coders of all levels – from beginners to seasoned pros. If one challenge doesn't quite spice things up for you, feel free to explore the variety of others available. New to CTFs? No worries – we cater to every skill level. Staying true to our Wizer Mission to make security awareness available to everyone, every developer can access these challenges at wizer-ctf.com. Dive into the world of secure code training with us – it's open and accessible to all!
But wait, There's More! Unlock a New Dimension: Wizer's Enhanced Secure Code Training for Developers!
While our public CTFs remain accessible to all, catering to widespread security awareness, we understand the unique needs of dev teams and security-driven companies. For those seeking comprehensive tracking of training progress and a dash of gamification, we have just the solution.
- XSS Mitigation
- SQL Injection Mitigation
- Server-Side Template Injection
- And More!
Our specialized developer-focused training videos go beyond the standard Boost library. By incorporating these unique resources, you'll not only enhance your team's coding skills but also unlock a private leaderboard exclusively tailored for your team. This personalized feature fosters skill expansion and encourages friendly competition among your developers.
Discover more about the advantages of Wizer's Secure Code Training for Developers and revolutionize your team's secure code training experience.
Ready To Learn to #CodeWizer?
- From Owasp 10 To Advanced Techniques
- Deep-Dive 1 new topic monthly
-
Fun CTF Challenges to apply learning

Ayelet HaShachar Penrod
A passionate security awareness advocate, I connect and support security professionals as a Community Manager while also managing customer accounts for **Wizer Managed**, our security awareness service. Driven by 4 years of learning from cybersecurity experts, I’m committed to making security awareness accessible to all—individuals, small businesses, nonprofits, and enterprises alike.