Top 5 Must-Know Phishing Simulation Templates - April Edition
Updated
Welcome to our monthly series featuring 5 Phishing Simulation Templates brought to you by the Wizer Phishing team.
It’s important that simulated phishes have a ‘why’; a reason beyond merely ‘seeing if my colleagues click’. Sometimes it can be to educate about a specific attack, and other times it can be to highlight how we respond when different scenarios are presented to us. Once you have your why, a solution like Wizer's Boost can let you customize your phishing campaigns for security awareness training with an easy-to-use and customizable phishing simulator.
Simulated phishing that includes a 'why' can be more creative than cruel - there’s a lot we can understand in our behavior when the intent is to educate and not trick. So let's see what that can look like.
Phishing Template: new Mentor Program from HR
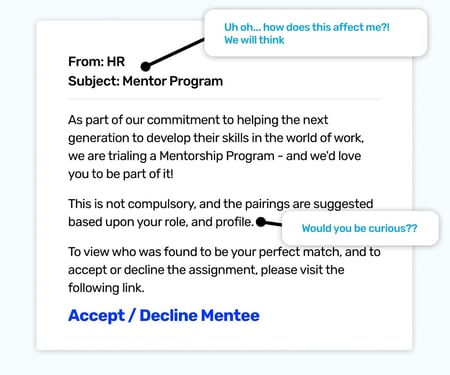
This template is the perfect example of a creative phish; it may not be seen in the wild, but the ingredients can be found in a multitude of phishing emails.
So what are the ingredients? Let's start from the top.
Firstly it’s from HR, which is such an abused identity because it’s both trusted and rarely ignored. Next, we have the subject line. This is like the title of a story that’s about to unfold. The curiosity hook is in the title - 'Mentor Program'. Immediately we’re programmed to start figuring out how this relates to us, and how it might impact us.
As we move to the body of the email, we discover we’ve been matched with a mentee which the thought of might present mixed emotions. On the one hand, it’s flattering we’re seen as knowledgeable enough to be a mentor, but we might also be thinking about how busy we are and annoyed at anything else being heaped on to our many tasks.
Then we notice the final line that makes everything feel like it’s back in our control - to view our mentee and accept or decline the pairing, just a simple click can set things straight and allow us to move forward how we want.
And that’s a powerfully coercive tactic. It’s combining curiosity with a feeling of control.
There aren't many people who wouldn’t really want to see who has been assigned to them and the simple call to action includes a way to prevent this entire 'story' from interrupting our lives any longer by stating it can be declined.
These are all the experiences someone who clicks this email could go through, and by sharing the story of the ‘magic trick’, we can get better at spotting the ingredients that create risk next time.
Phishing Template: Meeting Prep - See Attached!
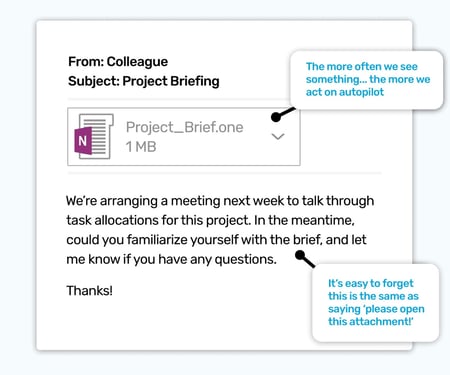
You’re standing at the sink, washing some plates. Someone walks up and passes you another plate, and what do you do? Exactly. You take it and submerge it into the suds. It’s a reaction that seems to bypass all decision-making processes, and it’s part of the autopilot we all employ at times to keep our thinking for the important things.
Now imagine you’re at work, and yet another email comes in where a colleague has shared a file. It’s almost instinctual for you to click and view it; like being passed a plate, or an unopened envelope, the next stage can happen almost without us realizing.
And this is why phishing simulations that mimic the main file-sharing service an organization uses are an extremely good way to educate about the extra dangers they possess because they are undoubtedly going to be one of the most dangerous phishes a colleague could receive.
These types of requests immediately tap into the natural reactions that have built up over time, and awareness needs to be raised in as constructive a way as possible.
Educate your employees how to identify and avoid phishing attacks with Wizer Boost.
Phishing Template: The Handy 'Undo' Feature
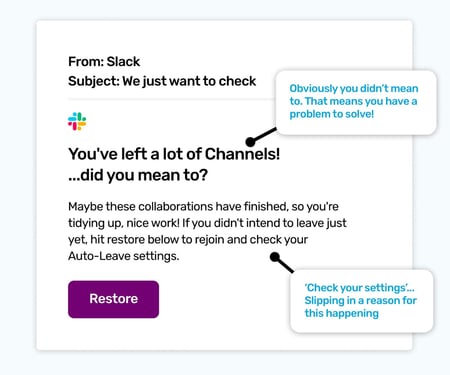
A fairly common theme of phishing emails is they turn up with a made-up problem conveniently presenting the cure to easily remedy it. That’s exactly what this Slack email sets out to do - pretend a load of channels were just deleted.
Now it would take a brave person to just ¯\_(ツ)_/¯, and think that it’s just what the universe must want. Most people, when they haven’t explicitly deleted something, get a little anxious when they think an incorrect setting could have done it for them. This email is absolutely playing on that with problem -> solution. And as there is a call to action that says, so helpfully, ‘Restore', we'll likely think, 'Awesome! Easy fix. Maybe I will get rid of them… but for now, I’ll just make my world all nice and keep it as it was before I saw this email."
One other important aspect of this email is it plays on the fact we can never know every function and setting we make within an app. Even if we did, we also know things get added, changed, or removed. This means problems don’t have to be true to be effective, they just have to kinda sound true.
Phishing Template: DNS Disaster
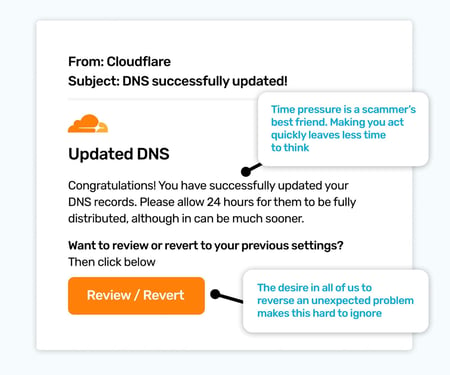
All of our inboxes are unique. It’s a meeting place for services, people, and newsletters that won’t let us unsubscribe, all to have a moment of our attention. This means that not all emails that are pretending to be niche identities will be plausible to everyone. Much like the last email template we mentioned - if an org didn’t use Slack, few if any people would pay it much attention.
The usual way to get more specific with simulations, and to avoid sending an irrelevant phish to too many people, is to break down your campaigns by department. This particular phishing template is a perfect example of that, intended for those with a more technical or even security-focused disposition. The formula may be recognizable now, it’s that tried and tested formula of = problem + solution.
In this case, the email is from Cloudflare, and it is congratulating you on your DNS settings being updated. Which would be awesome if you’d just updated them, but as we know, phishing emails are the work of fiction so no action on your part triggered it. And that begs the question… if you haven't updated the DNS… WHO HAS!!??
Now because it’s fake, no one has. But that’s not how our minds work, because they love stories, so it would be entirely normal to start to wonder if someone with malicious intent, like a hacker, had managed to change them.
Thankfully, there’s a lifeline! That all-important button to restore the settings to how they were. Phew. But as we know, if it was a genuine phish, this could be where the problems actually start. No matter how security aware you might be, or how technical, it’s a great learning experience to find out how we react to certain scenarios.
Phishing Template: Email Account Deactivation
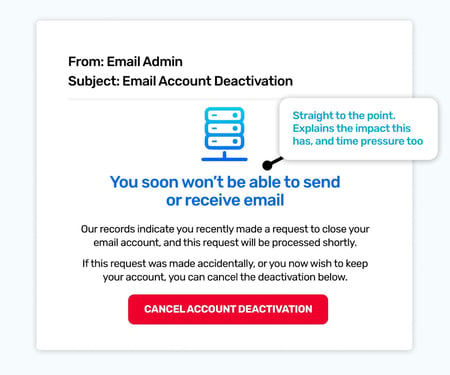
If you’re starting to see a pattern here… all this doom-mongering, then you’ve absolutely spotted one of the cyber criminals' main tactics. Turn up with a problem! All the problems!
It might seem heavy-handed, but we have to remember these emails will be dropping into a normal busy day, which is why we can be caught off guard so easily. This is actually a classic phish in the scamming world, but still extremely useful as a simulated phish.
It's important to note that a high click rate wouldn’t immediately mean there are huge problems. Rather, it could indicate some supplementary training is needed to cover some of the more basic tactics. It might even illustrate that some colleagues are unsure of the technical side of the services they use. Sometimes threats can be believable because we aren’t knowledgeable enough to question what’s been said.
As with all of these phishing simulation templates, getting a click can be a real opportunity to learn how we missed details - and that could be because we were struggling to read our phone in the sunlight! But by aiming for progress over perfection we can all make safer decisions over time.
Download these Phishing Templates to use in a security awareness training session
Ready to launch your next phishing campaign? Register now for a free 10-day trial of Wizer Boost to explore all of Wizer’s Phishing Simulation Templates and Phishing Exercises.
That's it for this month's phishing template ideas - looking for more ideas for phishing templates? Check out resources below ⬇️ And check back next month for more!
Past Phishing Templates:
Top 5 Must-Know Phishing Simulation Templates - March Edition
Top 5 Must-Know Phishing Simulation Templates - February Edition
- Pre-set Phishing Calendar for 2023
- Customizable Phishing Template Editor
- 100+ Phishing Templates
- Weekly Progress Reports